My view into your eBay - the eBay XSS flash
exploit
Geändert am 12.03.2008
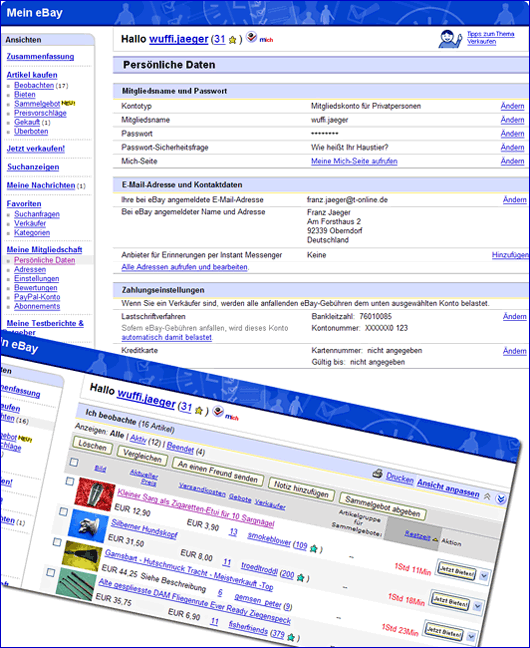
Criminals can access data of eBay members by using a security gap. Unsuspecting victims simply need to visit a specific eBay listing, no additional link must be clicked. During viewing the item page his/her name, address, E-Mail address, and other data can be submitted to third parties.
The function has been demonstrated by »falle-internet.de« by using a specifically prepared listing:
By integrating a flash animation into an item description it is possible through so-called Cross Site Scripting (XSS) to view all personal data which normally should be exclusively available to users in My eBay.
Besides the personal data also all latest trading activities (successful or not) as well as the watched items can be viewed. Also the personal mailbox My Messages is accessible.
In My eBay is shown:
- Name and complete address
- E-Mail address
- Bank data for Direct Pay (partly x-ed)
- Credit card data (partly x-ed)
- Additional information for password verification
- List of won / bought items
- List of Didn't win items
- List of watched items
- All messages sent and received through the eBay system in My Messages
These sensible information can be easily used by criminals to send fraudulent offers to unsuspecting victims, e.g. those ill-famed faked Second Chance Offers (SCO's). If these fake SCO's show the real data of the receiver, the trust of victims in the genuineness of such offers is considerably higher.
Also the criminal phishing of passwords is made relatively easy by this XSS security gap. By manipulation of certain listing elements a fake login page is presented to the victims, which forwards entered passwords to the criminal attackers. The deception is more perfect than the usual forwards to external sites it is possible to fade in the fake login directly to the listing page, the victim gets the impression that he/she is still on an official eBay page.
JavaScript and XSS
Each logged-in eBay member, on who's computer the Flash plugin is installed, and who has allowed JavaScript, can become victim of this security gap. The test showed that data scripting is possible completely unrecognized by the victim.
And so the view into the personal sphere of My eBay works:
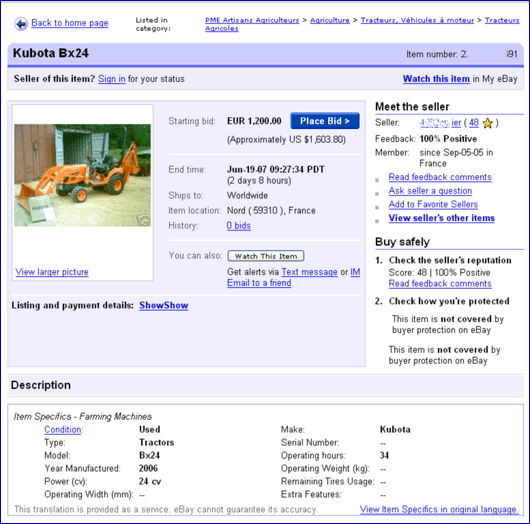
The criminal lists a rather prominent item on eBay, with a specially prepared Flash animation embedded into the item description. If a logged-in user visits this page his browser loads the malicious code of the scammer. This contains JavaScript which sends the eBay cookies of the user to the criminal. This import of external codes is already known since years as Cross Site Scripting (XSS).
As the Flash file is executed only on the computer of the victim user, eBay is unable to check the listing on prohibited JavaScript executables. eBay members can protect theirselves by generally disabling JavaScript in their browser, however, in that case the use of normal eBay pages is heavily influenced, important functions will not work without JavaScript.
The criminal lists a rather prominent item on eBay, with a specially prepared Flash animation embedded into the item description. If a logged-in user visits this page his browser loads the malicious code of the scammer. This contains JavaScript which sends the eBay cookies of the user to the criminal. This import of external codes is already known since years as Cross Site Scripting (XSS).
As the Flash file is executed only on the computer of the victim user, eBay is unable to check the listing on prohibited JavaScript executables. eBay members can protect theirselves by generally disabling JavaScript in their browser, however, in that case the use of normal eBay pages is heavily influenced, important functions will not work without JavaScript.
XSS: Security gap with tradition
The problems of (inter)active web contents is well-known to commercial internet players. Also eBay had to react in 2004 when the JavaScript security gap which was known already since one year finally had been proven and made public by the German magazine Spiegel. Before that eBay considered JavaScript in listings of their customers only being a »theoretical security gap«.
With their »Revised policy on use of script functions« eBay Germany reacted on October 1, 2004. Since then e.g. scripting of cookies, forwarding to other internet offers, implementation of external scripts and pages, or pop-ups are prohibited. However, the use of Flash for implementation of external content was excluded specifically from this prohibition.
Already then the German IT news service Heise wrote: »Since long developers and commercial vendors consider Cross Site Scripting as weak point in web servers and applications due to missing code filtering. Attackers infiltrate JavaScript into the victims´ browsers in order to get the authentification cookies. But the attacker had to play via cushions at eBay he gets the necessary tools free at hand.«
Malicious use documented
Scamming gangs are quite at home in the techniques of JavaScript and XSS, and use dangerous Flash codes since long in fraudulent eBay listings. The problem should be known to eBay, because already one year ago members of »falle-internet.de« reported such listings to the auction house.
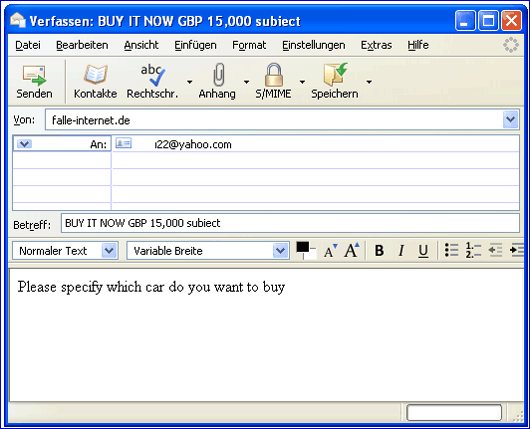
The variations of proven listing manipulation have increased considerably. One frequently used version is the manipulation of listing description in the browser of the viewer. Pending auctions are changed into Buy-it-now listings, actual high bids are falsified, or seller´s feedback details are changed by overlay. Rather common is also the script which opens a mail window once the user clicks anywhere in the listing:
The scammer´s E-Mail address and the reference line is filled in already in order to support contact by the victim:
Further examination clearly shows preparations for additional scamming attempts by insertion of Flash files:
Even further goes a special manipulation of the »Bid« button which has been noticed already rather frequently. If a user intends to bid on the item, he/she will be transferred to an external fake login site, from which the phished password is directly mailed to the scammer.
To bait a large number of victims the criminals regularly use attractive layouts or frequently asked items:
By clicking such interesting offer the victim is automatically transferred to the external fake login form:
All member logins and passwords typed in there are automatically mailed to the phisher.
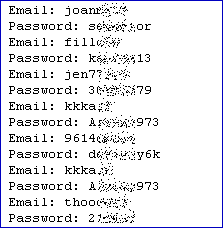
Within a few days only hundreds of account details are phished and ready for use by the scammers.
Proof by falle-internet.de under real conditions
3 months after we submitted specific information to eBay, and after more than one year knowledge about the real usage of the security gap by scammers, no effective reaction was performed by eBay. »falle-internet.de« therefore believes it is necessary to inform the public about this threat.
During research how criminals make use of eBay´s lacking security measures, »falle-internet.de« performed a practical demonstration test of the XSS Flash exploit under real conditions. Selected users could repeat the test, and they established that their personal data in My eBay had been accessible to third parties.
In November 2007 eBay got a confidential hint about our scheduled test series, as reaction »falle-internet.de« received an E-Mail from eBay Germany´s director »Law Enforcement Affairs« which could be considered as threat as it refers to the so-called Hacker Act, §202c of the German crime law.
Despite the fact that the danger by XSS is known since years, in early December »falle-internet.de« introduced the weak points including potential solutions to eBay Germany's »Law Enforcement Affairs« department. Mid December we also informed their department »Trust & Safety« again about the potential risks. Until today they are not removed effectively.
Recommendation
Until closure of the security gap we only can recommend not to use JavaScript or Flash when viewing eBay listings. When using Mozilla Firefox this can be solved by the browser add-on NoScript "; the Internet Explorer can be adjusted by using its Zone Model Zone Model
"; the Internet Explorer can be adjusted by using its Zone Model Zone Model .
.
Other internet platforms may be effected in a similar way, if they allow users the uncontrolled integration of Flash.
 "; the Internet Explorer can be adjusted by using its Zone Model Zone Model
"; the Internet Explorer can be adjusted by using its Zone Model Zone Model .
.Other internet platforms may be effected in a similar way, if they allow users the uncontrolled integration of Flash.